What is an Enterprise Cybersecurity Audit?
Why Conduct a Cybersecurity Audit?
Conducting an enterprise cybersecurity audit provides invaluable insights into the potential threats that may compromise your organization’s cybersecurity. Here is what you will get after conducting an audit with our team:
Validate your existing security controls and configurations
A cybersecurity audit will evaluate the effectiveness of your current security measures and configurations, helping you understand whether they are adequate to protect your organization from potential threats and improving your ability to prevent attacks.
Understand the potential impact of an attack on your organization
Our experts will analyze the potential outcome of a successful breach on your entire organization when each security risk present in your systems is exploited by an attacker, enabling you to prioritize remediation efforts and allocate resources efficiently.
Identify & fix all your cybersecurity risks
Our team will identify all existing vulnerabilities and security risks currently present across your organization, allowing you to systematically address these issues, strengthen your overall security posture and reduce your overall risk exposure.
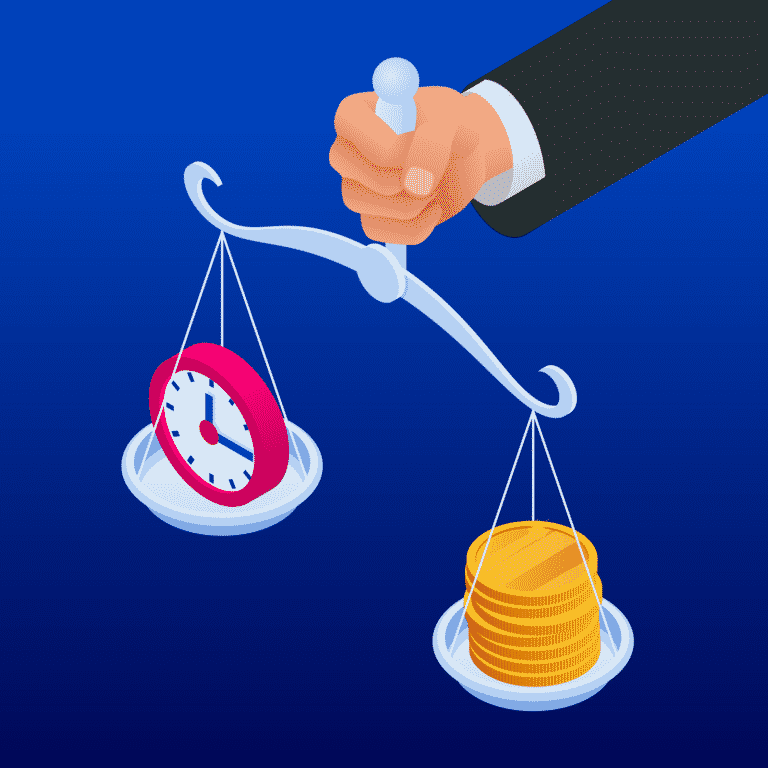
Get prioritized budgetary & resource allocation recommendations
After uncovering all cybersecurity risks present across your organization, our services will provide a list of prioritized action items including required budget and team members, helping effectively allocate resources on the most important risks faced. Our audits will help you optimize your cybersecurity budget and identify the key areas to invest in to prevent your most significant risks of facing a breach.
When Should You Perform a Cybersecurity Audit?
- Annually, as part of a proactive security strategy
- After major system or infrastructure changes
- Following a security incident or breach
- As part of a regulatory or compliance audit
- In response to new threats targeting your industry
- Prior to an M&A transaction or other major business event
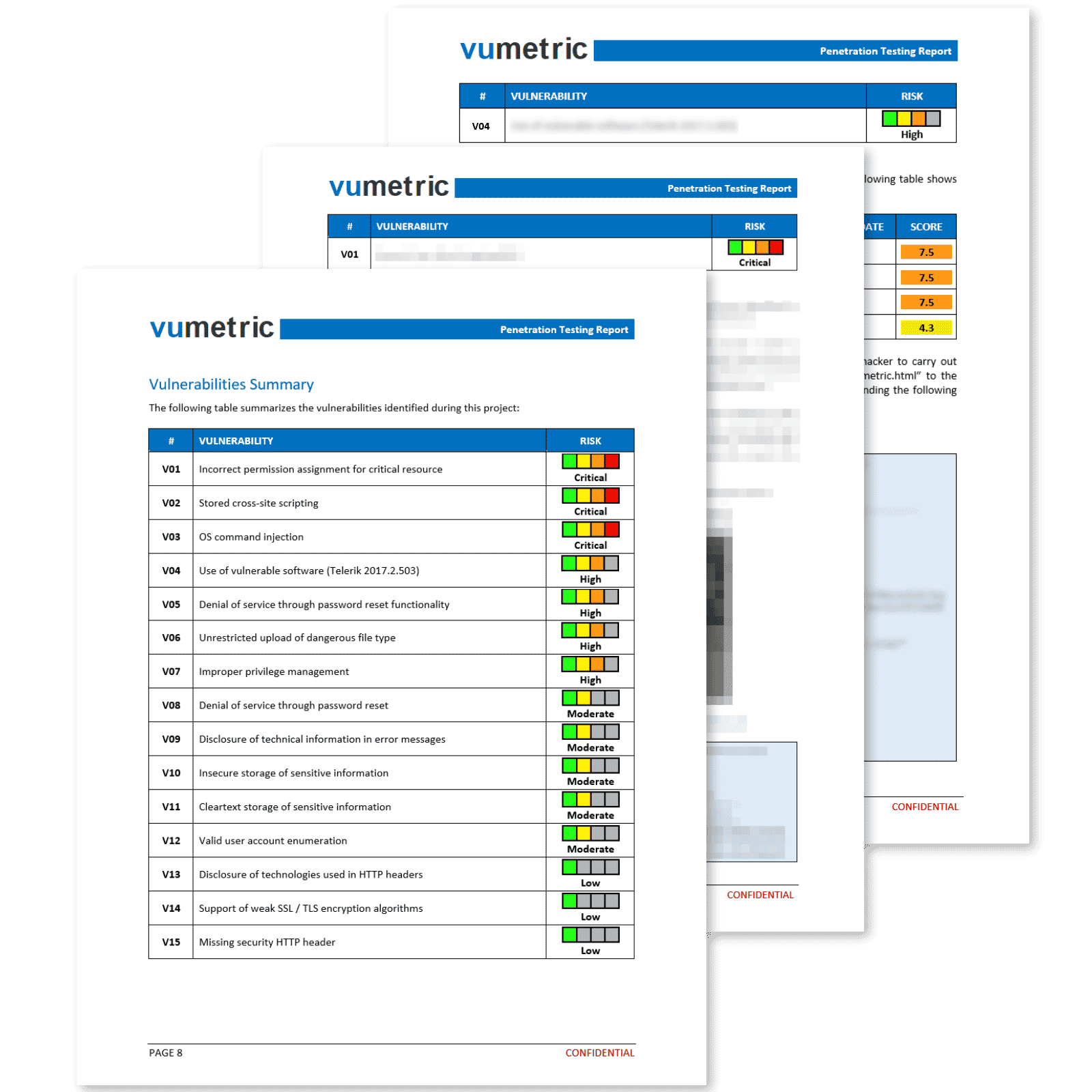
Common Cybersecurity Risks Identified
Inadequate access controls & permissions
Inadequate access controls and permissions enable unauthorized users to access sensitive systems and data. This service examines access control policies and permission settings, identifying weaknesses and providing recommendations for implementing least-privilege access principles to minimize the risk of unauthorized access.
Ineffective monitoring and logging
Ineffective monitoring and logging can lead to delayed detection of security incidents and hinder incident response efforts. This service assesses the organization’s monitoring and logging practices, identifying gaps and providing recommendations for implementing comprehensive monitoring and logging solutions to enhance detection and response capabilities.
Insufficient network segmentation
Lack of proper network segmentation can enable attackers to move laterally within an organization’s network, gaining access to sensitive systems and data. This service evaluates the current network architecture and provides recommendations for implementing effective network segmentation to limit an attacker’s ability to compromise additional systems.
Missing or misconfigured security controls
Organizations may have insufficient or misconfigured security controls, leaving them exposed to threats. This service identifies gaps in security controls and provides recommendations for proper configuration and implementation, ensuring a comprehensive defense against cyberattacks.
Unprotected critical assets
Critical assets, such as sensitive databases or high-value servers, may be inadequately protected, leaving them vulnerable to attacks. This service identifies unprotected critical assets and provides recommendations for implementing appropriate security measures, including encryption, access controls, and intrusion detection systems, to safeguard these valuable resources.
Unsecured data storage and transmission
Unsecured data storage and transmission expose sensitive information to potential theft or tampering. This service assesses data storage and transmission practices, identifying vulnerabilities and recommending encryption, secure protocols, and other best practices to protect sensitive data.
What's Included in Our Enterprise Cybersecurity Audits
Password & Access Management

Network & Cloud
Security
Governance &
Security Policies
Server
Security

Workstation
Security

Mobile & Remote
Work

Email
Security

Backup &
Restore
Cybersecurity Risks are Increasing
$3.5M
Is the average cost of a data breach incident.
63%
of breaches involve weak or compromised passwords.
300,000
new malware strains are created and spread daily.
266
average days to detect and contain a data breach.
87%
of senior managers admitted accidentally leaking data.
Cybersecurity Budgets Are Increasing
58%
of companies increased security budgets
82%
plan on hiring new security staff
81%
feel pressure to lower security costs
The Main Benefits of Conducting a Cybersecurity Audit
Better understanding of current security gaps and necessary improvements
Assistance to plan your cybersecurity roadmap
Get management buy-in and the necessary budgets for each measure
Optimize security spending by targeting relevant threats
Obtain the guidance needed to become or remain secure
Elevate your security in terms of compliance and best practices
Need Help To Assess And Improve Your Cybersecurity?

Frequently Asked Questions
Couldn’t find the information you were looking for? Ask an expert directly.
The purpose of this service is to identify and evaluate potential cybersecurity risks and vulnerabilities within an organization’s IT systems, providing insights and recommendations to enhance overall security posture and mitigate threats.
The process typically involves an initial assessment of the organization’s systems and infrastructure, followed by a detailed examination of specific areas, including hardware, software, and personnel. The auditor identifies potential threats and vulnerabilities, evaluates their impact, and provides recommendations for remediation.
To get started, you should gather details about your IT environment, key stakeholders, and any compliance requirements. You should also prepare necessary documentation, such as network architecture maps and security policies. It’s also important to identify a point of contact in your team that can provide technical details regarding your organization.
Yes, in most cases, we require access to various systems, networks, devices and configurations to conduct a comprehensive assessment. Any access and permissions requirements will be discussed with your team before the project launch.
This service is a crucial component of a robust cybersecurity strategy, as it helps identify weaknesses, assess potential threats, and develop actionable plans to improve security measures and mitigate risks.
Key stakeholders, including IT and security personnel, as well as senior management, should be involved in the assessment process to ensure thorough understanding and support for the recommended improvements.
The duration of the assessment depends on the size and complexity of the organization’s IT infrastructure. Smaller assessments may take a few days, while comprehensive audits may last several weeks.